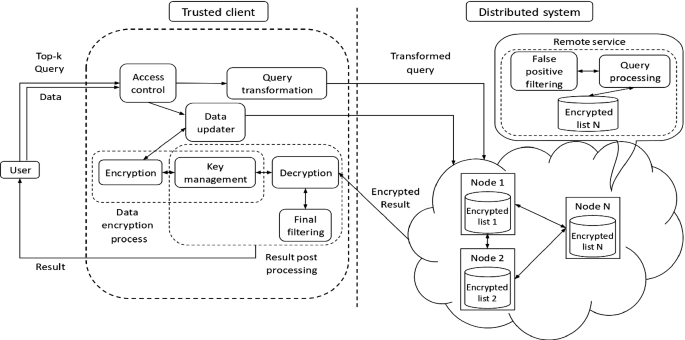
Electronics | Free Full-Text | Privacy-Preserving Top-k Query Processing Algorithms Using Efficient Secure Protocols over Encrypted Database in Cloud Computing Environment

Examining the Additivity of Top-k Query Processing Innovations | Proceedings of the 29th ACM International Conference on Information & Knowledge Management
![PDF] Effective top-k computation in retrieving structured documents with term-proximity support | Semantic Scholar PDF] Effective top-k computation in retrieving structured documents with term-proximity support | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/23ae867fdc9c88741f973c205a57ccf7a1d30901/3-Figure2-1.png)


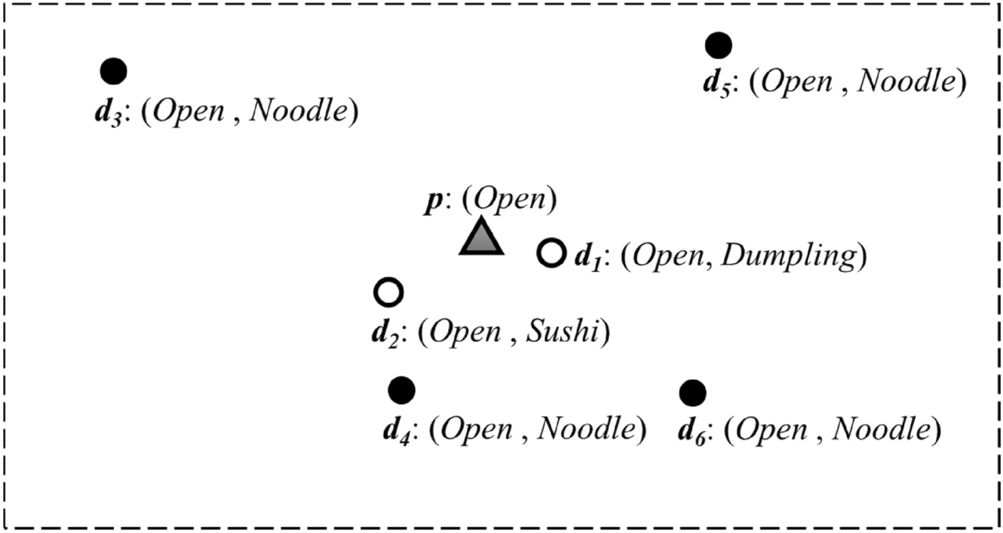
![PDF] Branch-and-bound algorithm for reverse top-k queries | Semantic Scholar PDF] Branch-and-bound algorithm for reverse top-k queries | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/40afc88eaa8eaf8b29ba859cbae39672731d90bf/1-Figure1-1.png)